Yesterday Fox News posted an article with the title, “Here’s why Hillary Clinton losing her security clearance matters for the rest of us.”
The article explains:
Hillary Clinton no longer has a security clearance. A letter released from the Department of State to Senator Chuck Grassley, a Republican from Iowa, says she lost her clearance on August 30 at her request. The State Department also withdrew security clearances from five people Clinton had previously requested clearances for, as she had designated them “researchers.” One was Cheryl Mills, who was once the deputy White House counsel for President Bill Clinton who defended him during his 1999 impeachment trial. The names of the others were redacted.
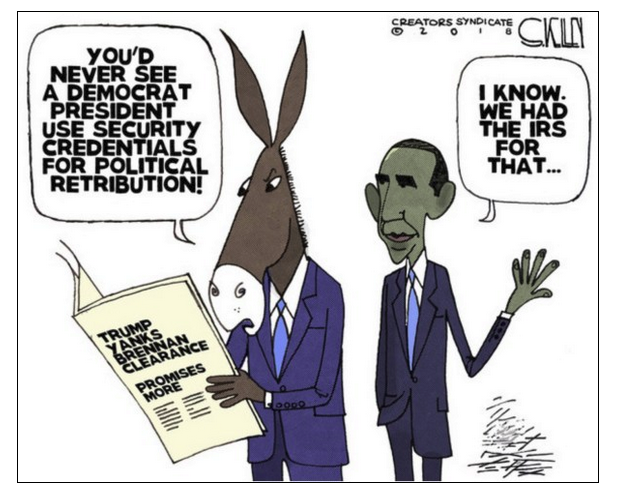
The mainstream media is treating the loss of these clearances as a move by Clinton to avoid a political snub by the Trump administration.
The article points out that Hillary Clinton should have lost her clearance when it was discovered that she had classified information on her private servers. Unfortunately, Hillary’s servers were not the only problem.
The article continues:
For instance, the group of House IT aides who made up what amounted to a spy ring didn’t even have to undergo background checks to get their insider positions—jobs that allowed them to see and copy all of the emails and more from the members of Congress they worked for.
Evidence shows that Imran Awan, the head of the group who was an IT aide working for Rep. Debbie Wasserman Schultz, a Democrat from Florida, was spying on congressmen and even congressional staffers. A current IT aide who wants his name kept out of print told me Awan even used his own email address as the Apple IDs when setting up staffer’s phones.
“The only reason I can think of for why Imran would do that is this would have given him the ability to see everything these staffers were doing,” said the House IT aide, a contracted employee who has more than a decade of experience working for congressmen.
This IT spying scandal, however, was covered up – as it only had to do with Democrats in Congress, the mainstream media apparently had no interest in pursuing the story.
But this lax security is not simply a political story. It puts every one of us in jeopardy. A congressman whose private emails or other data are in the hands of someone who can blackmail or otherwise influence them is a risk. For all of us. And without public pressure, it’s next to impossible to know whether Congress has tightened security to prevent this kind of spying from taking place.
There is a more recent incident:
Only weeks ago, a volunteer on the staff of a member of the U.S. House of Representatives, Jackson A. Cosko, was arrested after Capitol Police became aware the Wikipedia pages of three U.S. Senators had been edited to include restricted personal information without their knowledge or permission.
“On the night of Oct. 2, 2018, according to the affidavit,” says a Department of Justice press release, “a witness saw Cosko at a computer in the office of a U.S. Senator who had once employed him. The witness confronted Cosko, who left the office. An investigation led to Cosko’s arrest by the U.S. Capitol Police.”
If Cosko hadn’t posted the information, as he is alleged to have done, for political purposes (called “doxxing”) but had instead used it privately or even gave it or sold it to a news agency or a foreign government, he might never have been arrested. Or he might have gotten off just as Imran Awan and his associates did.
The article reminds us that private companies do a much better job of internet security:
What other employer allows former employees to access their networks? Companies commonly terminate employees email accounts and access before they even tell them they’ve been let go.
The government needs to learn the lesson that private companies have already learned.